As a private investigator, you know how easy it is to track someone’s location. For instance, placing a GPS tracking device on someone’s vehicle (in states where it is legal). Tracking software will then be used to monitor the movements of that vehicle. Similarly, investigators can use mobile spy software to track a mobile phone’s location (and other activity). So, given the relatively simple process of tracking others, how does a PI prevent someone from tracking them? That’s where a Faraday bag can help protect devices against electromagnetic interference, preserve electronic devices, and shield against hacking attempts.
What is a Faraday Bag?
A Faraday bag prevents radio waves from entering or escaping from an electronic device. For example, some hackers install viruses, malware, or other software on phones via a Wi-Fi signal. Often, the device is a mobile phone, tablet, or laptop computer. However, other devices include car key fobs, garage door openers, smart watches, credit cards, etc.
The outer material is usually made of ballistic-grade nylon. On the inside, there are multiple layers of high-shielding Titan RF fabric. Typically, they are water-resistant but not waterproof.
Who Uses Faraday Bags?
Although Faraday bags sound like something reserved for a special ops agent, anyone can use them. However, the military, government, and law enforcement officials often use them. In addition, corporate executives use them to prevent the theft of corporate information while traveling. Also, private investigators can use them to keep someone from tracking their mobile devices.
What kind of signals do they block?
Although the quality and functionality of the bags may differ by manufacturer, most bags block:
- Radio waves
- Bluetooth signals
- Wi-Fi
- Cellular signals, including 5G
- GPS tracking signals
- Electromagnetic field (EMF) reduction
- Radio Frequency Identification (RFID) tags
Military Use
The military uses Faraday bags in various ways to protect electronic equipment and information from electromagnetic interference (EMI) and electromagnetic pulse (EMP) attacks. Here are some examples:
- Protecting communication devices: Communication is essential in military operations, and any disruption to communication can have severe consequences. Faraday bags protect communication devices such as radios, smartphones, and laptops from EMI and EMP attacks, ensuring communication is not disrupted during critical missions.
- Shielding weapons and explosives: EMI and EMP can disrupt Electronic triggering systems in weapons and explosives. Faraday bags shield these devices from such attacks, ensuring that they function correctly when needed.
- Securing sensitive information: The military uses Faraday bags to protect sensitive electronic devices, such as laptops and USB drives, that contain classified information from eavesdropping and hacking attempts. Faraday bags prevent electromagnetic signals from leaving the bag, making it difficult for hackers to intercept and steal information.
- Protecting electronic medical equipment: Military medical personnel use electronic equipment to monitor the health of soldiers in the field. Faraday bags protect these devices from EMI and EMP, ensuring that they function correctly when needed.
Using Faraday bags, the military can ensure that communication is not disrupted, that weapons and explosives function correctly, and that sensitive information is secure.
Corporate Use
Corporations use Faraday bags to protect electronic devices and information from electromagnetic interference (EMI) and electromagnetic pulse (EMP) attacks. Here are some examples:
- Protecting electronic devices during travel: Many employees travel with devices such as laptops and smartphones, which may contain sensitive corporate information. Faraday bags protect these devices from EMI and EMP attacks during travel, ensuring that the devices function correctly when needed.
- Securing sensitive information: Corporations use Faraday bags to protect sensitive electronic devices such as laptops and USB drives that contain confidential information from eavesdropping and hacking attempts. Faraday bags prevent electromagnetic signals from leaving the bag, making it difficult for hackers to intercept and steal information.
- Protecting against data breaches: Faraday bags can also be used to prevent data breaches in the workplace. For example, employees working on a laptop containing sensitive information can place the laptop in a Faraday bag when they leave their desks. This ensures the laptop is protected from hacking attempts and unauthorized access when the employee is absent.
- Securing mobile payments: With the rise of mobile payments, corporations use Faraday bags to protect payment terminals from EMI and EMP attacks. By using Faraday bags, corporations can ensure that mobile payments are secure and that customer information is protected from hackers.
Different Types of Bags
Small Bag: Mission Darkness Non-Window Faraday Bag
| Preview | Product | Price | |
|---|---|---|---|

|
Mission Darkness Non-Window Faraday Bag for Phones // Signal Blocking Faraday Cage Prevents Hacking… |
$25.00 |
View on Amazon |
This military-grade bag is made of ballistic nylon that is water-resistant (not waterproof). Inside, there are two layers of high-shielding TitanRF Faraday Fabric. It blocks WiFi, Bluetooth, cell, GPS, RFID, and radio signals. Regarding capacity, it has plenty of room for multiple cell phones, credit cards, and more.
As of this writing, the item is the highest-rated bag on Amazon. It has a rating of 4.7 out of 5 stars from over 4,500 customers.
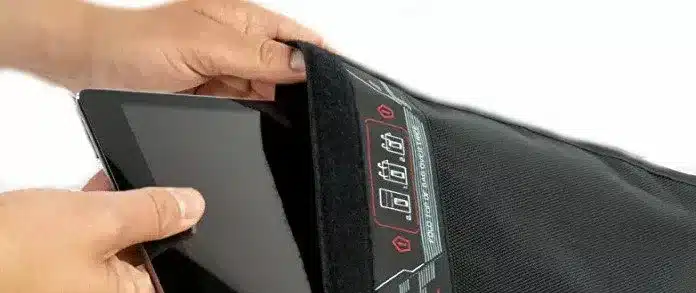
Medium Bag: Non-Window Faraday Bag for Tablets
| Preview | Product | Price | |
|---|---|---|---|

|
Mission Darkness Non-Window Faraday Bag for Tablets // Device Shielding for Law Enforcement… |
$55.00 |
View on Amazon |
Also, from Mission Darkness, this black nylon bag is water-resistant. It provides the same signal-shielding capabilities as the smaller bag. However, it has a greater storage capacity. This means you can store more mobile devices or protect a tablet. In addition, it has a unique serial number to use for asset tracking.
Large Bag: X2 Faraday Duffel Bag with a detachable pouch
| Preview | Product | Price | |
|---|---|---|---|

|
Mission Darkness X2 Faraday Duffel Bag + Detachable MOLLE Faraday Pouch (Gen 2) // Military-Grade RF… |
$299.00 |
View on Amazon |
Believe it or not, you can get the same RF shielding for your larger electronic devices with this handy duffel bag. Again, you get the same quality protection, and this one has much more storage space. You can store multiple laptops, two-way radios, GPS units, or other bulky devices. The detachable pouch is great for smaller items when you don’t need the whole bag.
This one is a bit pricier than the small bags. However, it would help to consider the value of the information and data you protect.
It has a rating of 4.6 out of 5 stars from more than 200 customer reviews.
Best Selling Products
Questions and More Information
If you have any questions or comments, please post a message below. If you purchased one of the items above, please let us know your thoughts. However, please direct any customer service issues to Mission Darkness.
- Insurance Fraud Investigations - April 1, 2026
- The Magnum P.I. Private Investigator Legacy: Defining a Profession - April 1, 2026
- Genealogy for Private Investigators - April 1, 2026